Cyber Security
Idealshields is a Leading Cyber Security Solution Provider. We bring you a world-class set of consulting, next-generation products, and customized training to help your organization protect against cyber attacks. Our sheer and laser-sharp focus on Cyber Security, coupled with the vast knowledge and experience of our leadership team ensure that you get the very best quality from Idealshields.
What WeOffer?
Our certified consultants, who fully understand the latest cyber risks and challenges, are here to assist you in implementing the cybersecurity controls based on your needs. Contact us now for further details.

Security Assessment Services
By mimicking the actions of an actual attacker, we exploit weaknesses without putting the organization in actual jeopardy and allow the organization to address each weakness accordingly.

Managed SOC Services
We offer a fully managed Security Operations Centre (SOC) capability that allows our customers to focus on running their businesses without the hassle of building and maintaining their own SOC.

SIEM
Cydea SIEM provides comprehensive monitoring capability for an organization’s entire infrastructure, to enable the security operations team in detecting and responding to threats.
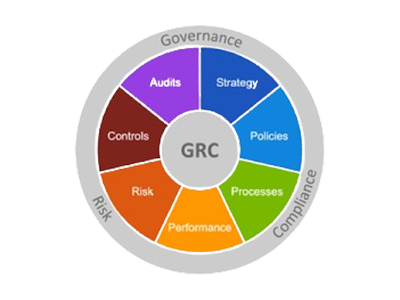
Governance, Risk & Compliance
We offer a comprehensive assessment of your organization’s security posture, identifying potential gaps and ensuring compliance with regulatory requirements across all business locations.
DFIR Services
Our Digital Forensics & Incident Response services can help organizations respond, investigate & remediate effectively. We can uncover intrusions, evict attackers and recover business operations.

Red Team Services
We will simulate an attack against your network, showing you exactly how your people, and security protocols will perform when it comes to protecting your organization against a cyber-threat.

Email Phishing Simulation Service
Our Comprehensive Simulated Email Phishing service enables organizations to identify and mitigate phishing threats by assessing how employees respond to
malicious emails.

Deception Platform
CDP is a single platform with integrated modules capable of deploying and monitoring decoys, identifying breaches, and capturing complete forensic data of an advanced threat actor’s TTPs.

Threat Intelligence Platform
CTIP collects threat feeds from numerous sources and integrates them thereby enabling security analysts to make business decisions that are intelligence- driven.